AI agents are accessing enterprise systems right now — without identity, without agent controls, and without governance or audit trails.
AI Agents Are Everywhere. Without Governance or Audit Trails.
No inventory
Most security teams cannot list the AI agents operating inside the enterprise, what they access, or which team deployed them.
No access controls
AI agents reach ERPs, CRMs, and databases with broad permissions. No per-agent, per-tool boundaries exist.
No audit trail
When the board asks which AI agents accessed what data — there is no record, no attribution, no answer.
What Fortune 1000 IT and Security
Leaders Are Saying
Enterprise security and IT executives on why Aizome matters.

“Aizome is demonstrating a lot of value in controlling AI Agents with a comprehensive Identity led approach. Clearly we cannot do it ourselves, nor leverage any of our existing tools.”
- CISO, Fortune 500
“Aizome provides a unique approach to discovery of AI Agents, as well as making them accountable.”
- VP AI Security, SANS Institute

“Aizome helps organizations embrace AI Agents usage by employees while keeping it safe, same as we did with BYOD.”
- Ex CIO & CISO, Top 20 Global Retailer

“Everyone will develop Agents at our organization, and Aizome can play a critical role in enabling it — connecting to any system without restrictions while not losing control.”
- CIO, Leading US Online Bank

“Aizome is demonstrating a lot of value in controlling AI Agents with a comprehensive Identity led approach. Clearly we cannot do it ourselves, nor leverage any of our existing tools.”
- CISO, Fortune 500
“Aizome provides a unique approach to discovery of AI Agents, as well as making them accountable.”
- VP AI Security, SANS Institute

“Aizome helps organizations embrace AI Agents usage by employees while keeping it safe, same as we did with BYOD.”
- Ex CIO & CISO, Top 20 Global Retailer

“Everyone will develop Agents at our organization, and Aizome can play a critical role in enabling it — connecting to any system without restrictions while not losing control.”
- CIO, Leading US Online Bank

“Aizome is demonstrating a lot of value in controlling AI Agents with a comprehensive Identity led approach. Clearly we cannot do it ourselves, nor leverage any of our existing tools.”
- CISO, Fortune 500
“Aizome provides a unique approach to discovery of AI Agents, as well as making them accountable.”
- VP AI Security, SANS Institute

“Aizome helps organizations embrace AI Agents usage by employees while keeping it safe, same as we did with BYOD.”
- Ex CIO & CISO, Top 20 Global Retailer

“Everyone will develop Agents at our organization, and Aizome can play a critical role in enabling it — connecting to any system without restrictions while not losing control.”
- CIO, Leading US Online Bank
Become the Next BYOD
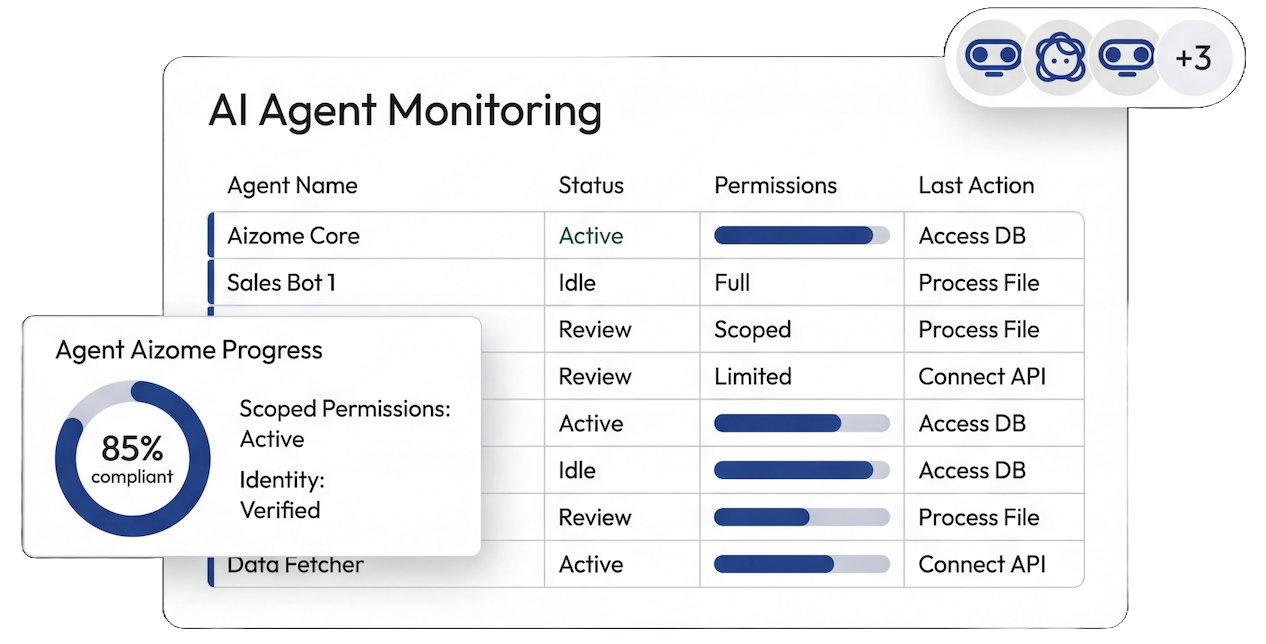
Full Agent Inventory
Every AI agent mapped — what it is, what it accesses, what actions it takes. One unified view across the entire organization.
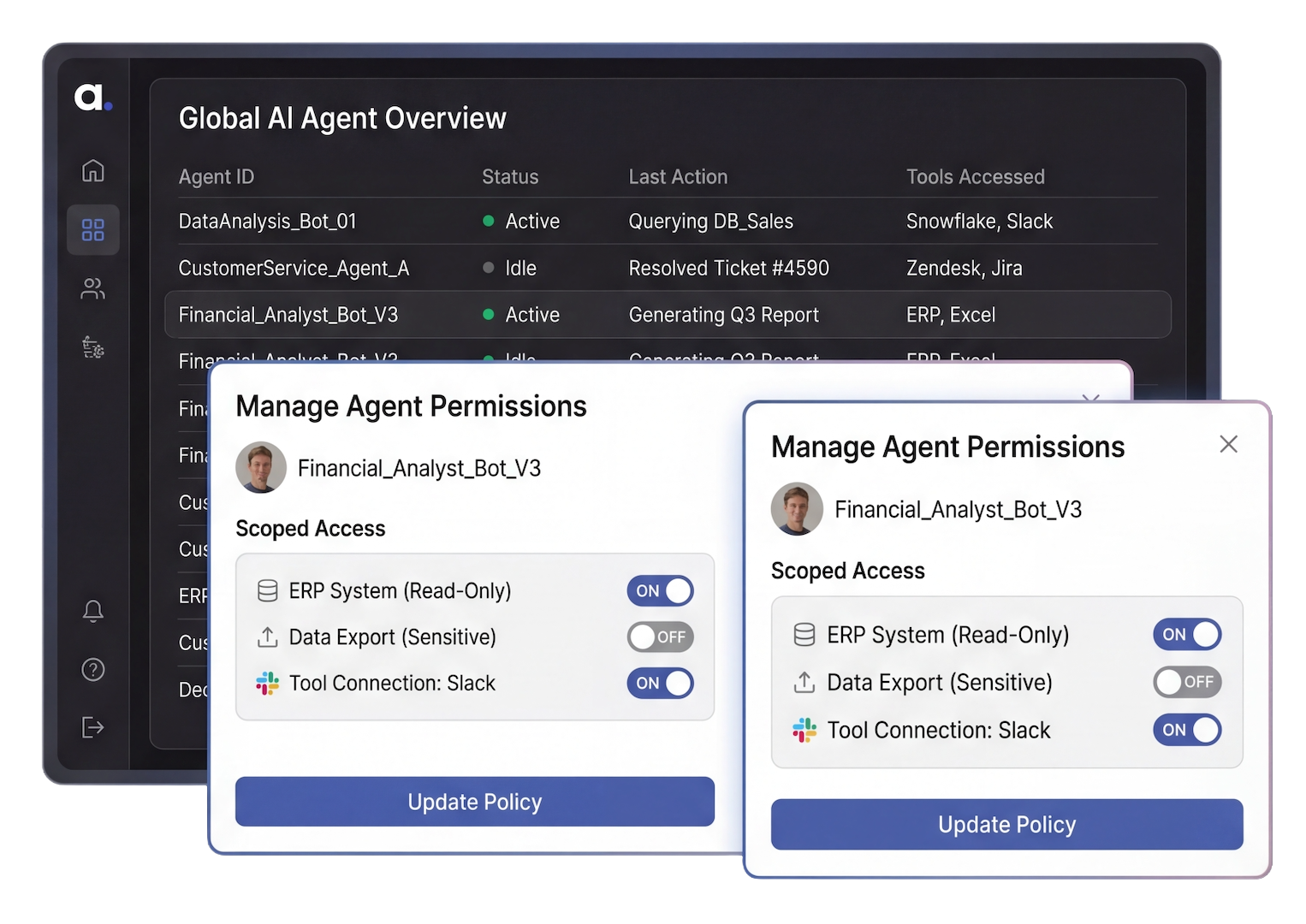
Agent Identity Controls
Per-agent, per-tool, per-action access controls. Enforced automatically. No over-privileged agents.
Be an Enabler to AI Adoption
Enable every employee in your organization to easily build agents that reach ERPs, CRMs, HR platforms, and legacy databases — even those without MCP or agent APIs — while you stay in control at all times.
Complete Governance & Audit Trail
Every agent action logged with identity, tool, timestamp, and outcome. Immutable. Attributable. Board-ready.
Connects to Every Tool in Your Stack
ERPs, CRMs, HR platforms, databases, cloud infrastructure — even legacy systems without MCP or agent APIs.
Explore the Platform















































































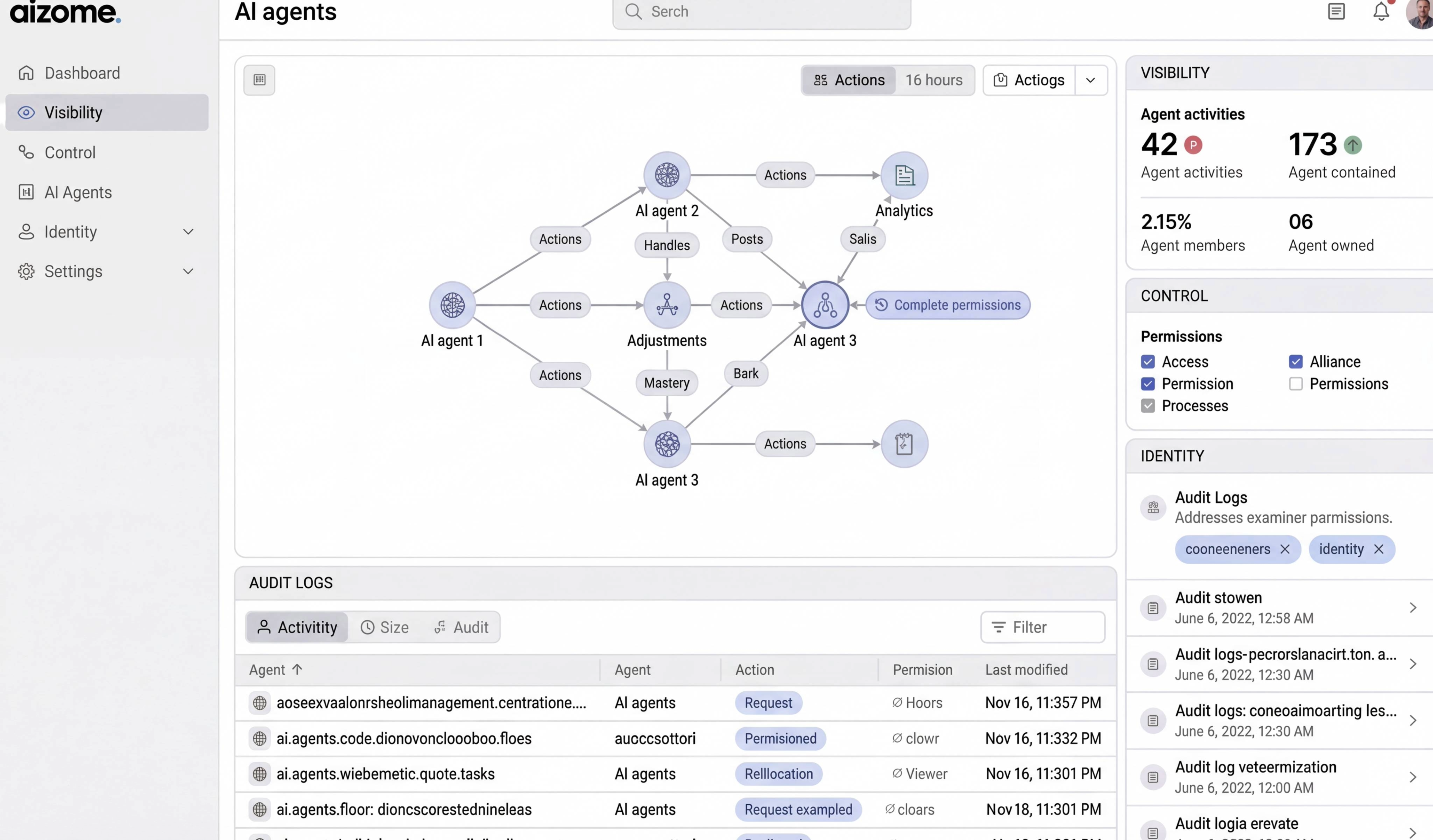


Make AI Agent Control Become the Next BYOD
See how Aizome maps every agent, enforces permissions, and delivers the audit trail the board requires.